STATION DC Cybersecurity Meetup
Security First: Reflections from the STATION DC Cybersecurity Meetup
 On April 7th, Sarrene Miller, Founder and CEO of TGS Tech, attended the STATION DC Cybersecurity Meetup in Washington, DC, a morning gathering of founders, security engineers, operators, investors, and public sector leaders working across the cybersecurity ecosystem. The conversations that morning were direct, technically grounded, and in several cases, uncomfortably honest about where the industry still falls short.
On April 7th, Sarrene Miller, Founder and CEO of TGS Tech, attended the STATION DC Cybersecurity Meetup in Washington, DC, a morning gathering of founders, security engineers, operators, investors, and public sector leaders working across the cybersecurity ecosystem. The conversations that morning were direct, technically grounded, and in several cases, uncomfortably honest about where the industry still falls short.
About STATION DC
STATION DC is a non-profit tech hub located in Washington's Union Market District, launched by Capital Factory in partnership with the District of Columbia. Its mission is to connect frontier-tech founders, investors, military leaders, and policymakers in the same room to solve problems that matter at a national scale. Operating as a physical clubhouse and convening space at 1323 4th Street NE, it hosts programming spanning AI, energy, security, and dual-use innovation, work that sits deliberately at the intersection of private sector capability and federal policy. Partners and members include startups, venture capital firms, non-profits, government agencies, and corporate leaders, all operating within a network designed to give innovators direct access to the relationships and policy intelligence that DC uniquely provides. For a company like TGS Tech, operating out of the DC metro area and building infrastructure targeting enterprise and government-adjacent industries, it is exactly the right room to be in.
The SOC 2 Conversation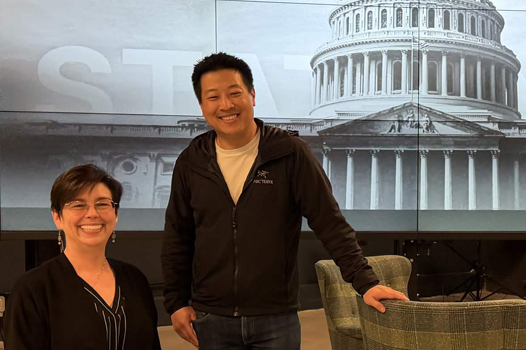
A recurring theme throughout the morning was SOC 2 certification, specifically, the gap between companies that treat it as a checkbox exercise and those that treat it as a genuine reflection of their security posture. The distinction matters more than it might appear. SOC 2 is not a product you buy. It is an audit framework that examines how your organisation handles security, availability, processing integrity, confidentiality, and privacy across your systems and operations.
The companies in the room who had been through the process, and those who had audited others, were consistent in one observation: the organisations that struggle most are the ones that start thinking about security only when a client or investor demands a report. By that point, the gaps are structural, not cosmetic, and closing them under audit pressure is a significantly more expensive and disruptive exercise than building correctly from the start.
The Persistent Gap in Security Culture
 That observation led naturally into a broader conversation about security culture that felt familiar to anyone who has worked in enterprise technology for more than a few years. The tools have changed considerably. Threat detection, identity management, zero trust architectures, and cloud security tooling are all dramatically more capable than they were a decade ago.
That observation led naturally into a broader conversation about security culture that felt familiar to anyone who has worked in enterprise technology for more than a few years. The tools have changed considerably. Threat detection, identity management, zero trust architectures, and cloud security tooling are all dramatically more capable than they were a decade ago.
What has not changed with anything like the same speed is the underlying attitude in many organisations toward security as a foundational concern rather than a reactive one. Security operations, the people, processes, and disciplines involved in maintaining a defensible posture, still tend to be underfunded, undertreated, and undervalued until something breaks. The frustration in the room was palpable, and it was not theoretical. These were practitioners describing the reality of organisations they work with or audit regularly.
Ethical Hacking and the Value of Adversarial Thinking
One of the more productive threads of the morning centred on ethical hacking and penetration testing as tools for closing the gap between perceived and actual security posture. The argument is simple: you cannot defend a system you do not understand from an attacker's perspective. Ethical hacking, authorised, structured attempts to identify vulnerabilities before malicious actors do, is a standard component of a credible security programme and a formal requirement within several compliance frameworks including SOC 2. The conversation touched on how this practice is still treated with suspicion in some organisations, as though inviting scrutiny is itself a risk, when the opposite is true. An organisation that has never stress-tested its own defences has no reliable basis for claiming it is secure.
Why This Matters for TGS Tech
TGS Tech is building Apex Engine as an enterprise-grade platform targeting AEC, digital twin, and simulation industries, sectors that handle sensitive project data, proprietary designs, and in some cases infrastructure-relevant information. Security is not an afterthought in that context. It is a prerequisite for any serious enterprise client conversation, and it is a prerequisite we are building toward deliberately.
SOC 2 and ISO 27001 compliance are active items on our roadmap, and the security infrastructure work underway in Phase 3 of the Apex Engine development programme reflects the same principle that came up repeatedly at the STATION DC meetup: security built in from the architecture level is categorically different from security bolted on after the fact. The conversations on April 7th reinforced that the right approach is also, ultimately, the only defensible one.